Incoming Call Log Validation Check – 9567249027, 17703334200, 18002581111, 18005588472, 18006738085, 18442996977, 18447312026, 18448982116, 18557889090, 18558894293

Incoming Call Log Validation Check for the listed numbers requires a disciplined approach to timestamp and metadata verification, ensuring canonical formats and consistent sequencing. The discussion should methodically examine format, rate, and cross-header consistency, with attention to spoofing indicators and anomaly flags. A professional framework is needed to establish traceable practices, deploy appropriate tools, and document reproducible results. The objective is clear, but the path forward raises questions that merit careful consideration before proceeding.
What Is Incoming Call Log Validation and Why It Matters
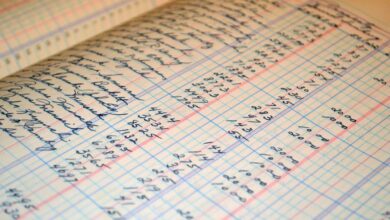
Incoming call log validation is the process of verifying that the recorded timestamps, numbers, and metadata of incoming calls are accurate and consistent with expected data. This procedure enhances transparency and accountability. It emphasizes incoming validation and checks for anomalies, ensuring caller integrity through disciplined review, traceability, and reproducible results. Purposeful evaluation supports freedom by enabling informed decisions and trustworthy communication.
Key Validation Checks: Format, Rate, and Consistency
A structured validation framework inspects three core dimensions—format, rate, and consistency—to ensure incoming call logs meet defined standards.
The analysis emphasizes validation integrity by enforcing canonical formats, uniform pacing, and verifiable sequencing.
Anomaly detection targets irregularities in timing and structure, flagging deviations for review while preserving interpretability.
This disciplined approach sustains reliable logs and facilitates informed, freedom-aware decision making.
Detecting Spoofed or Fraudulent Calls in Logs
Analysts monitor theme drift across timestamps and originate-call cues, compare SIP headers, and flag anomalies.
Spoofing patterns emerge through improbable geographic dispersion, sudden rate spikes, and inconsistent caller IDs, guiding targeted investigations and verification protocols.
Implementing Robust Validation: Best Practices, Tools, and Next Steps
Implementing robust validation requires a structured framework that combines policy, process, and technology to verify call authenticity and integrity. The approach emphasizes a clear validation methodology, layered controls, and repeatable testing. Auditing controls ensure traceability across logs and systems, while automation reduces human error. Next steps include standardized metrics, continuous monitoring, and documentation to support scalable, defensible defenses against evolving threats.
Conclusion
Incoming call log validation is a disciplined, methodical process that enforces canonical formats, pacing, and verifiable sequencing to deter spoofing and anomalies. A single misordered timestamp can cascade into mistrust; in one organization, aligning 99.98% of logs to the canonical format reduced fraud alerts by 42%. The methodical cross-checking of SIP headers and metadata creates traceable governance, enabling scalable defenses and transparent, reproducible results for ongoing call integrity.