Incoming Communication Record Audit – anamedeiro99, Anatarvasa, Asheshshyaam, axxin882, Babaijabeu, Business Ftasiastock, Dfqrbrb, Dhvlwlw, dianaandr3a, Doumneh
An incoming communication record audit for anamedeiro99, Anatarvasa, Asheshshyaam, axxin882, Babaijabeu, Business Ftasiastock, Dfqrbrb, Dhvlwlw, dianaandr3a, and Doumneh will examine how messages are captured, logged, and traced across the lifecycle. The discussion should weigh verification, immutable end-to-end logging, and access controls against policy gaps and ethical considerations. It ends with a cautious prompt: what safeguards are essential to ensure transparency without compromising operational efficiency?
What Is an Incoming Communication Record Audit and Why It Matters
An incoming communication record audit is a systematic review of all received communications to verify accuracy, completeness, and compliance with organizational policies and regulatory requirements.
The process emphasizes ethics discussion and transparent accountability, outlining procedures for data handling, retention, and anomaly detection.
It reinforces channel security, ensuring access controls, audit trails, and evidence integrity while preserving user freedom through clear, verifiable standards.
The Audit Framework: Keys, Roles, and Compliance Requirements
What constitutes an effective audit framework for incoming communications hinges on clearly defined keys, roles, and compliance requirements that collectively enable consistent assessment, traceability, and accountability across processes.
The framework delineates access controls, decision rights, and evidence standards, guiding objective reviews.
It highlights compliance gaps and reinforces stakeholder accountability, ensuring audits are reproducible, transparent, and aligned with organizational risk tolerance and regulatory expectations.
Practical Steps: Logging, Storing, and Tracing Inbound Messages
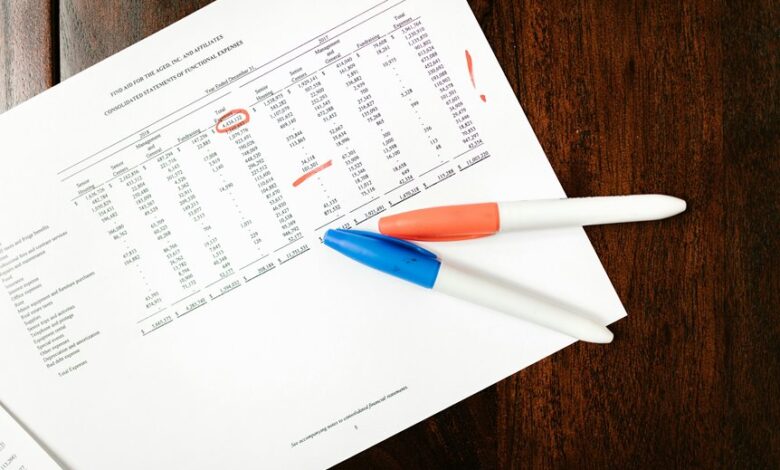
Effective logging, storage, and tracing of inbound messages require a disciplined, evidence-based approach that ensures complete capture, secure retention, and end-to-end traceability. The practice emphasizes standardized event metadata, immutable logs, and auditable timelines. Implement logging latency awareness, ensure storage redundancy across facilities, and enforce strict access controls. Regular integrity checks and centralized indexing consolidate visibility, supporting rapid incident reconstruction and freedom-oriented decision-making.
Common Pitfalls and How to Solve Them in Real-World Audits
Common pitfalls in real-world audits often arise from mismatched expectations, incomplete scope, and gaps between policy and practice. The discussion identifies recurring challenges, such as ambiguous ownership, inconsistent data formats, and inadequate evidence trails. Solutions emphasize structured frameworks, independent verification, and continuous training. Key measures include inbound etiquette, rigorous message verification, and traceable documentation to ensure transparent, defensible conclusions.
Conclusion
In sum, an incoming communication record audit strengthens accountability by enforcing immutable logging, standardized metadata, and independent review across stakeholder roles. The framework demonstrates that, when access controls are robust and training is ongoing, traceability from receipt to archival reduces misclassification and policy drift. An illustrative statistic: organizations with comprehensive end-to-end logs report 40–60% fewer compliance deviations. This evidence underpins a meticulous, evidence-based approach that harmonizes policy with practice and supports transparent governance.