Validate Incoming Call Data for Accuracy – 3533982353, 18006564049, 6124525120, 3516096095, 6506273500, 5137175353, 6268896948, 61292965698, 18004637843, 8608403936
Validating incoming call data for accuracy involves a careful assessment of each number: 3533982353, 18006564049, 6124525120, 3516096095, 6506273500, 5137175353, 6268896948, 61292965698, 18004637843, and 8608403936. The approach is analytical and disciplined, focusing on digit integrity, plausible country and area codes, and consistent formatting. It establishes a reproducible baseline, enabling proper routing and traceability. Yet the challenge remains: how will the workflow handle edge cases as systems evolve?
What Is Validating Incoming Call Data and Why It Matters
Validating incoming call data involves systematically confirming that each data element received from an external system is accurate, complete, and consistent with defined expectations. The process emphasizes validation principles and reliable data provenance to establish trust, traceability, and accountability.
This detached assessment highlights how structured checks reduce ambiguity, support informed routing decisions, and sustain interoperability across systems while preserving operational freedom and integrity.
Cleaning and Standardizing Numbers for Consistent Routing
As data validation confirms the integrity of incoming calls, attention shifts to cleaning and standardizing numbers to ensure consistent routing decisions across systems. The process evaluates cleansing patterns, normalizing formats, and removing non-numeric artifacts, enabling uniform interpretation.
Structured routing schemas rely on canonical representations, reducing ambiguity and mismatch risk across platforms while preserving flexibility for future schema evolution.
Detecting Anomalies and Authenticating Call Data in Real Time
The process relies on anomaly detection to flag deviations and data authentication to verify source integrity.
A precise, methodical framework enables immediate responses, reducing fraud risk while preserving operational freedom and trust in the validation ecosystem.
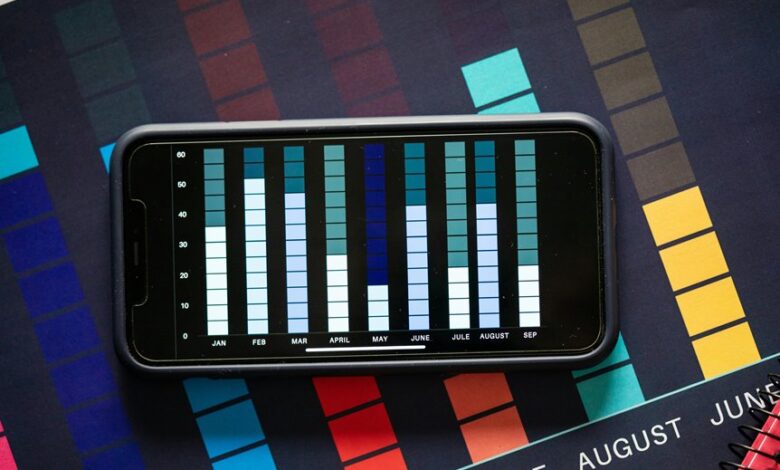
Implementing a Practical Validation Workflow (Tools, Rules, and Metrics)
How can a practical validation workflow be implemented with concrete tools, rules, and metrics to ensure accurate call data processing?
A systematic framework aligns data validation with defined rules, automated checks, and traceable audits. Real time monitoring detects deviations, while dashboards display KPIs. Tooling includes ETL validators, schema checks, and anomaly detectors; metrics measure completeness, accuracy, and latency for reliable data quality.
Conclusion
In the quiet hum of the validation pipeline, numbers flow like meticulous rivers, each digit inspected as if weighing stones for a bridge. Patterns appear, anomalies fade, and consistent formatting emerges from disciplined sorting. The data, now lucid and traceable, stands ready to route with confidence, its provenance anchored in verified integrity. With every pass, the system grows more trustworthy, a precise lattice where accuracy and interoperability reinforce one another, ensuring reliable communication across complex networks.





